Bandwidth Management and Optimization
Non-essential applications such as P2P downloading and online video are not only occupying staff’s productive hours, but can also be abusive which occupies significant amount and portion of bandwidth, leading to slow access to critical business applications, and thus low business productivity. Dealing with such network concern, Sangfor IAM is incorporated with the best-of-breed bandwidth management and optimization module to ensure corporate bandwidth is being utilized productively.
Flexible bandwidth management
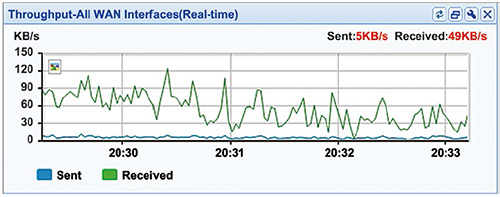
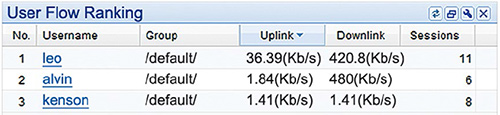
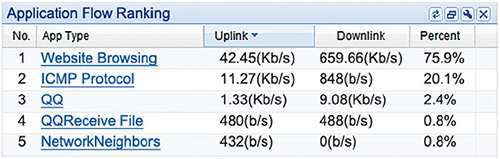
Having Internet access without bandwidth management is like having cars traveling on a freeway at various speeds without traffic rules and guidance – traffic congestion will occur. To manage and regulate the network traffic with desired settings, IAM dynamically assigns bandwidth to both uplink and downlink, by application/ file type/ website type/ user/ group/ schedule, keeping the network traffic in orders, and guarantee satisfactory performance for prioritized or critical business applications.
Dynamic Bandwidth Management
One limitation of static bandwidth management is that once bandwidth is being reserved for certain users, it became unavailable to others no matter in use or not. However, with dynamic bandwidth management mechanism, it enables bandwidth to be allocated in an optimal way among all users within one enterprise, adapting to the bursty nature of traffic flow, with the following feature:
“Bandwidth borrowing” when guaranteed bandwidth for specific applications/users is not fully utilized; Activate the BM policy once bandwidth utilization reaches a pre-defined level of usage; Allow average allocation or free competition options among users in one single traffic pipe; Separated bandwidth management for overseas network access from those for domestic use.
Intelligent P2P Identification and Control
P2P control has never been an easy task due to the varying, fast evolving, hopping and dynamic nature of P2P applications. However, with the unique P2P intelligent identification technology embedded in IAM, P2P control is no longer a problem, as enterprises are able to recognize and control both encrypted and unencrypted transmission, protecting the enterprise network from most P2P software.
Multi-line and Intelligent Routing
For organizations with multiple Internet access lines, user access performance is optimized by assigning an optimal line for the traffic. In case of line interruption, IAM will automatically route all traffic through the assigned optimal line.
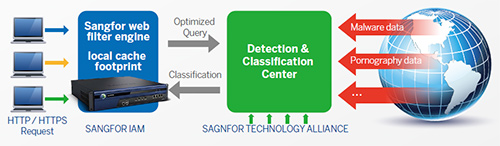
Proxy/ caching
Bandwidth is considered an expensive and valuable network asset for most enterprises, and all enterprises would expect this asset to be utilized productively. However, most enterprises are confronted with potential bandwidth waste with unmanaged networks. With such challenge in mind, Sangfor IAM was incorporated with Proxy/cache to reduce duplicated data using a unique “multi-weighted elimination algorithm” web caching technology. With this technology, frequently accessed Webpages, files and flashes are cached in the IAM appliance and once being cached, users would access data from the storage rather than loading all over again from the Internet, reducing 30-50% of Internet traffic and maximizing utilization.